RBAC User List
RBAC Users allows a permission-based management of the system. A user can have two types of permissions: ZAPI Permissions and Web GUI Permissions.
A user may access the Load Balancer as a member from a group through an API if they enable Zapi permissions and defined ZAPI KEY. The same is true for the Web GUI with his username and password if the user has Web GUI permissions or access to both.
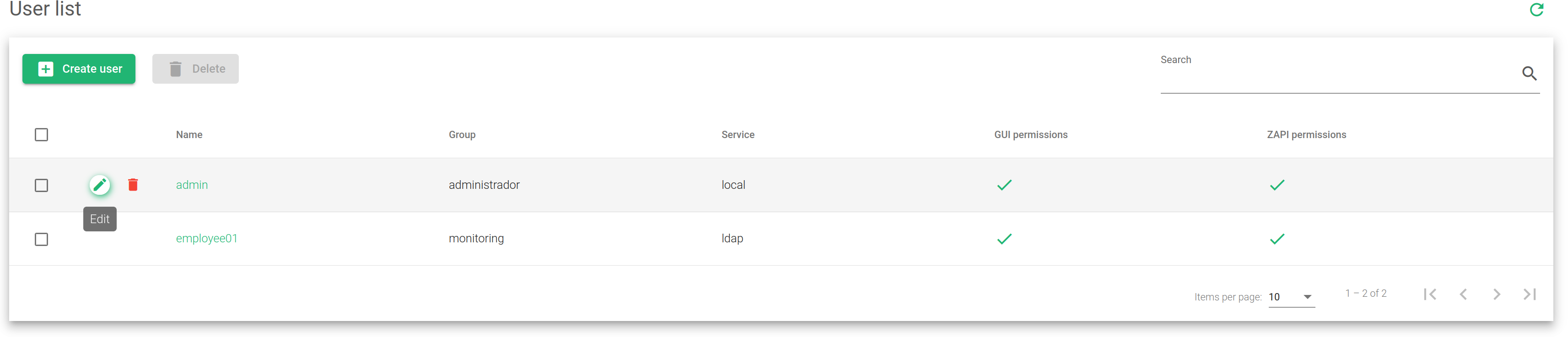
The image below shows a list of users with its properties. These properties have been described below.
Name. The label that easily identifies a user. This name is the same that is used to access the Web GUI.
Group. A group that a user belongs to. A user can only belong to one group.
Service. Defines whether the user will access locally or through a Light Weight Access Protocol(LDAP).
GUI Permissions. It indicates if the user has permission to log in to the Web GUI. The status indicators include:
- Green. The user is granted access to ZEVENET Web GUI.
- Red. The user is denied access to ZEVENET Web GUI.
ZAPI Permissions. It indicates if the user has permission to access the Load Balancer through ZEVENET API.
- Green. The user is granted access to use ZEVENET API.
- Red. The user denied access to use ZEVENET API.
Actions. Use the following actions to manage the user list.
- Create User. Opens the user creation form.
- Edit. Changes some values in the configuration form.
- Delete. Removes all the configurations of a user from the system.