Contents
RBL domains are domains that point to servers that maintain lists of IP addresses that have been flagged for malicious activity. This can include spammers, brute force attackers, and scraping robots.
In this section, you will learn how to Add or Remove your own custom domains to this list. If your company has a DNS server with a custom list of IP addresses that you want to block, you can use this section to do so.
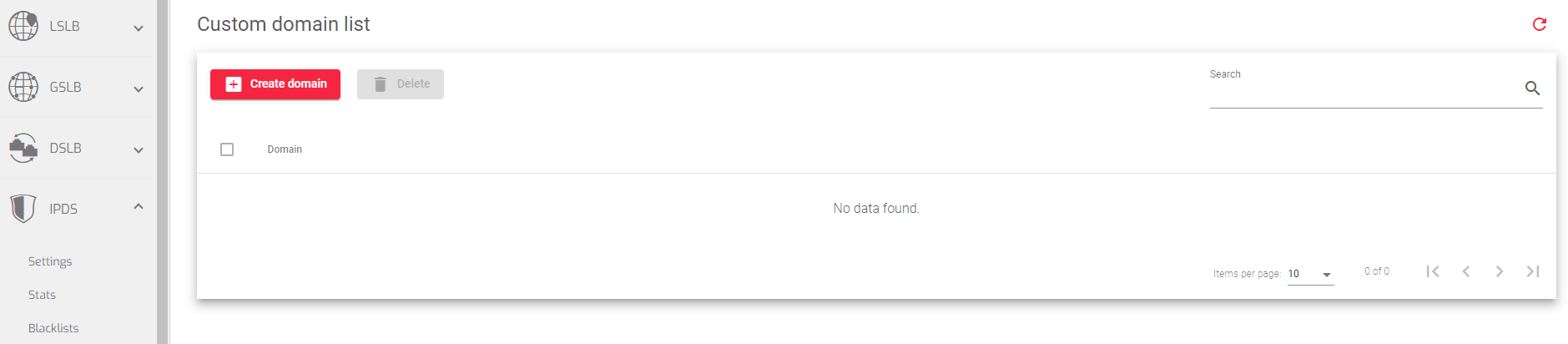
Custom Domain List
The Custom Domain List section allows you to add, delete, or edit your own custom domains. Each domain added should be a DNSBL.
When a mail server wants to check a client IP address against a DNSBL, it does the following:
- Reverses the order of the octets in the IP address.
- Appends the DNSBL’s domain name to the reversed IP address.
- Looks up the name in the DNS as a domain name (A record).
- If the name is found, the client is listed in the DNSBL.
- Optionally, the mail server can look up the name as a text record (TXT record) to get the reason why the client was listed.
Looking up an address in a DNSBL is similar to looking it up in reverse DNS, but it uses the A record type instead of the PTR record type, and it uses a forward domain instead of the special reverse domain in-addr.arpa.
How to create a custom domain.
To create a custom domain:
- Within the Custom Domain list section, click Create domain button.
- Enter the domain name in the Domain field.
- Click the Apply button.
Preloaded Domain List
The bottom section of the RBL Domains page shows a list of domains that are maintained and updated by the SKUDONET team. These domains are used by SKUDONET load balancers to check for malicious IP addresses.
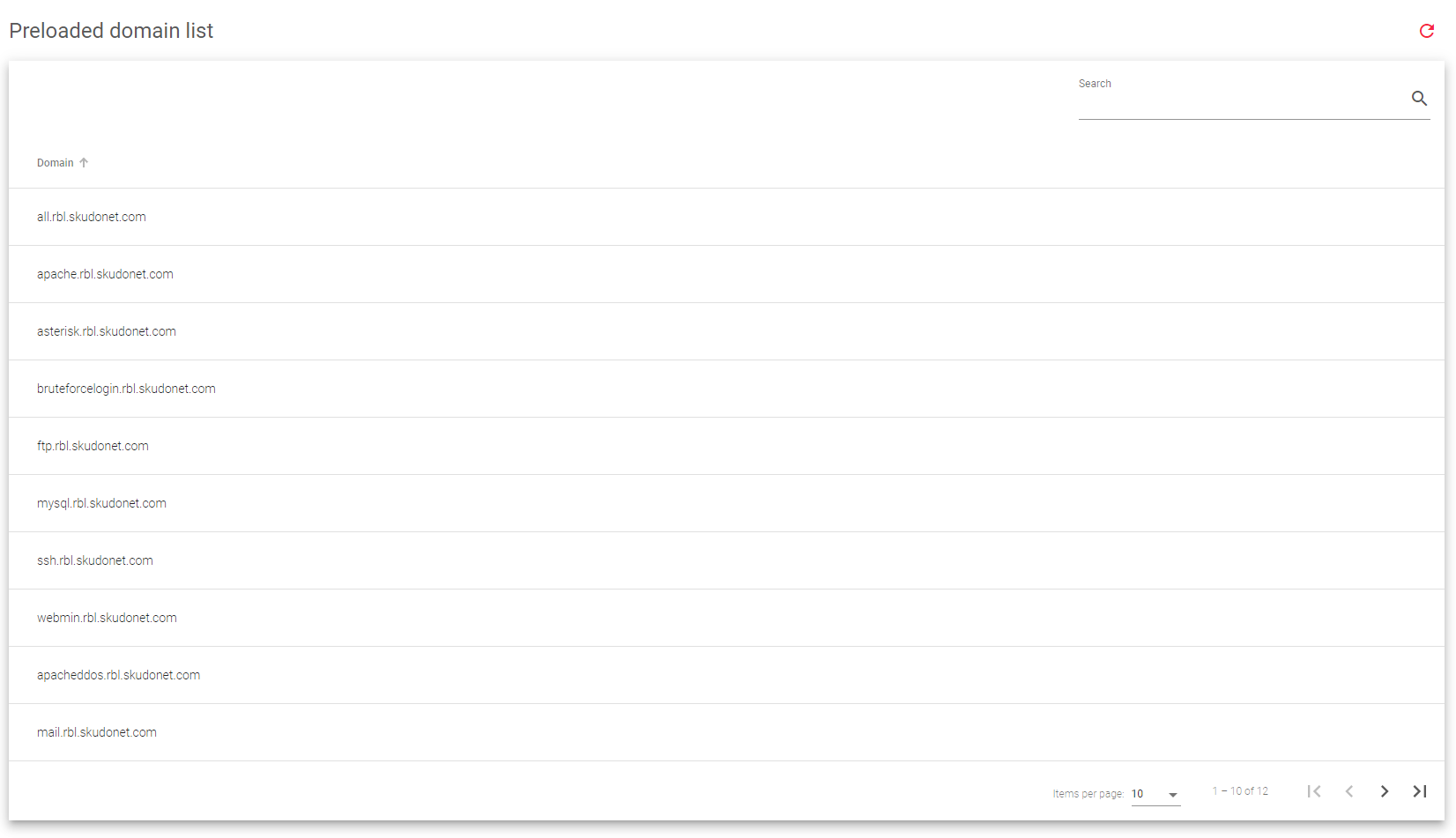
The SKUDONET DNS servers for RBL rules are ns1.rbl.skudonet.com and ns2.rbl.skudonet.com. Ensure that your load balancer can reach these DNS servers.
If you do not use the SKUDONET DNS servers, your load balancer will query a different DNS server (such as 8.8.8.8). This server will then resend the query to the final DNSBL server (such as blocklist.de).
SKUDONET keeps a mirror of the DNSBL from blocklist.de. This mirror is updated daily.
DNSBL queries
DNSBLs, or Domain Name System Blacklists, are lists of IP addresses that are known to be associated with spam or other malicious activity. Mail servers can use DNSBLs to check client IP addresses before accepting messages from them. If a client IP address is listed in a DNSBL, the mail server can block the message.
To check a client IP address against a DNSBL, a mail server reverses the order of the octets in the IP address and appends the DNSBL’s domain name. The mail server then looks up the name in the DNS as an A record. If the name is found, the client is listed in the DNSBL.
Here is an example:
Client IP address: 172.168.42.23 DNSBL domain name: all.rbl.skudonet.com Reversed IP address: 23.42.168.172 Lookup: 23.42.168.172.all.rbl.skudonet.com Result: Found
The result of the lookup tells the mail server that the client IP address is listed in the SKUDONET DNSBL. This means that the client IP address has been associated with malicious activity, such as hosting malware or phishing sites. The mail server can then block the message from this client.
DNSBL queries are a valuable tool for mail servers to use to help protect their users from spam and other malicious activity. By checking client IP addresses against DNSBLs, mail servers can block messages from known spammers and other attackers.
Next Article: IPDS | WAF | Rulesets

