Contents
Local Services
The Local Services section manages load balancing services, such as; HTTP, Web GUI, SSH, Rsyslog, and Global etc.
HTTP
This service is used to manage and operate the SKUDONET appliances. It is delivered over the HTTP protocol.
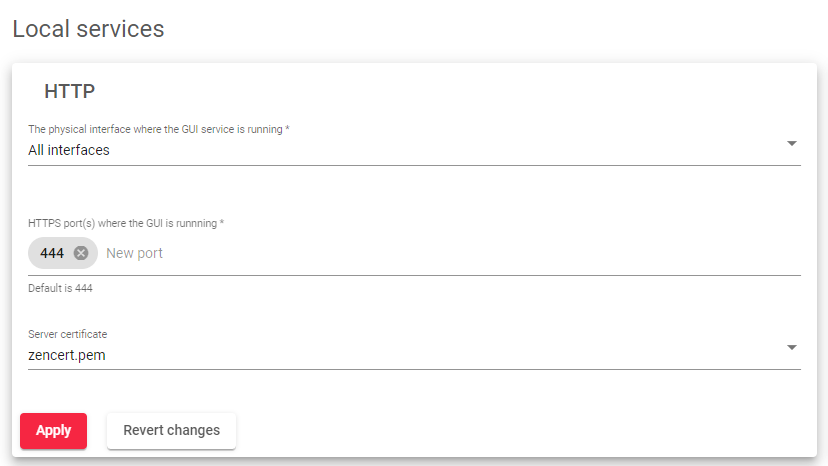
This service includes the following parameters:
- The physical interface where the GUI service is running: This is the interface where the web panel service is bound to all the physical, bonding, and VLAN interfaces configured in the load balancer. Virtual and floating interfaces are not recommended.
- HTTPS Port where the GUI service is running: This is the port used by the web GUI service for administrative and operational purposes. The default port is 444.
- Server certificate: This is the authentication certificate that shows a user has permission to use SKUDONET appliances.
After clicking the Apply button, you will need to confirm the changes in a popup window.
SSH
The SSH Management Service allows you to remotely access and manage your SKUDONET appliance using the SSH command-line tool. This service is essential for maintenance and cluster replication tasks.
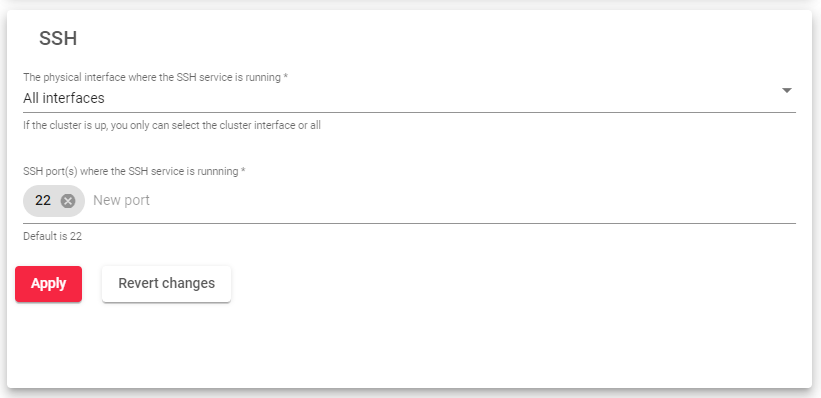
This service includes the following parameters:
- The physical interface where the SSH service is running: The SSH service is bound to a physical interface, such as an Ethernet interface. Virtual and floating interfaces are not recommended, as they may not be accessible remotely.
- SSH Port(s) where the SSH is running: The SSH service listens on port 22 by default. However, you can change this port in the SSH Management Service settings.
After clicking the Apply button to apply any changes you make to the SSH Management Service settings. The SSH service will be restarted automatically.
SNMP
The SNMP Monitoring Service allows you to integrate your SKUDONET appliance into a centralized SIEM (Security Information and Event Management) platform. This service is used to monitor your load balancer for potential security threats and performance issues.
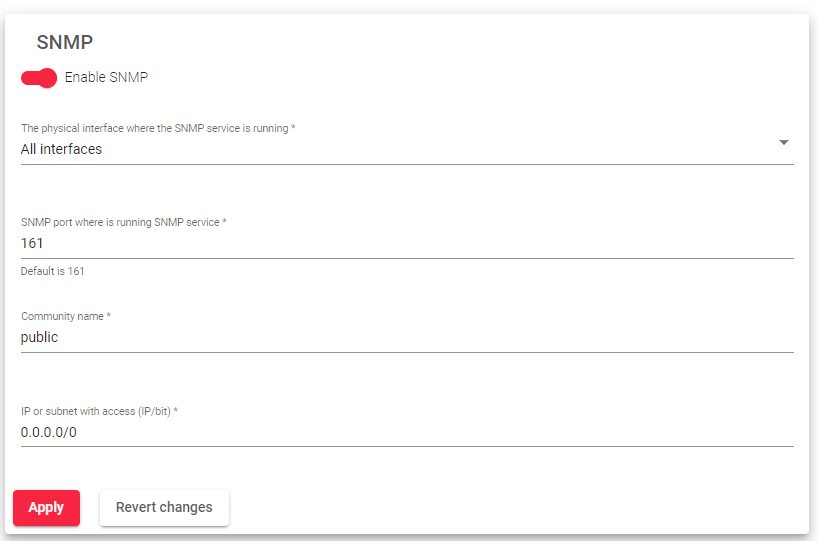
This service includes the following parameters:
- Enable SNMP: Check or uncheck the “Enable SNMP” checkbox. The service is disabled by default.
- Physical interface where the SNMP service is running: Select the physical interface where the SNMP Monitoring Service will be running.
- SNMP Port where is running SNMP service: Enter the port number where the SNMP Monitoring Service will be listening for incoming connections. The default port is 161.
- Community name: Enter the read-only community name that will be used to access the SNMP Monitoring Service. The default community name is “public”.
- IP or subnet with access: Enter the IP addresses or subnets of the clients that will be allowed to access the SNMP Monitoring Service. If you want to allow access from only one IP address, use a netmask of /32.
After clicking Apply button to apply all of your changes. The SNMP Monitoring Service will be restarted automatically.
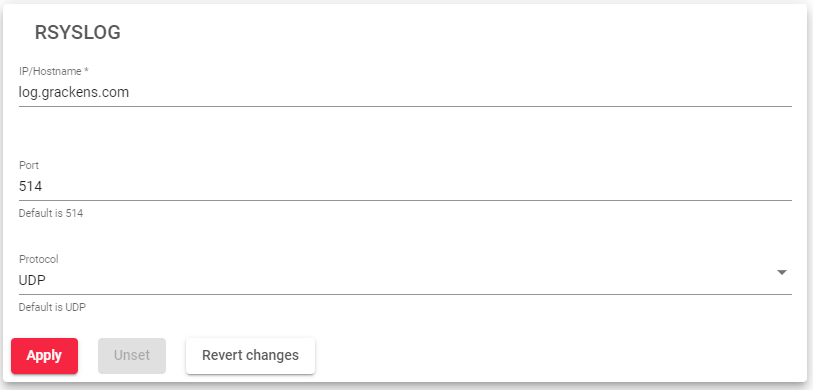
Rsyslog
IP/Hostname: This is the address of the Rsyslog server that you want to send your log files to.
Port: This is the port number that the Rsyslog server is listening on.
Protocol: This is the protocol that you want to use to send your log files. The two most common protocols are UDP and TCP.
Global
These services can be used to modify the load balancer to meet the specific needs of your organization.
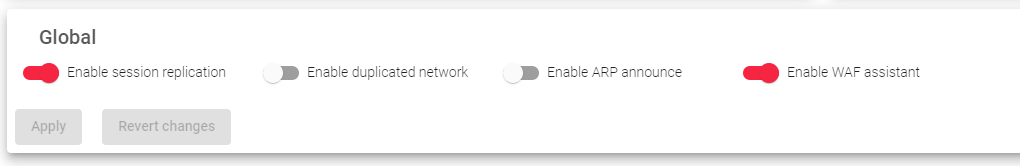
This service includes the following parameters:
- Enable session replication: When enabled, session replication ensures that if the master node fails, the new master will continue with the sessions and the user will not need to create a new one. This feature is part of the Stateful Cluster and is enabled by default.
- Enable duplicated network: Enabled duplicated network: SKUDONET does not allow you to configure the same network on multiple interfaces. However, this option allows you to configure the same network twice. If you disable this option, SKUDONET will ensure that your traffic does not create asymmetric routes. This option is disabled by default.
- Enable ARP announce: When enabled, an ARP announcement is executed to announce the MAC changes to the network every minute. This is also disabled by default.
- Enable WAF assistant: Enables a firewall to defend against and monitor attacks on the HTTP protocol.
After clicking the Apply button, all these services will be added to the Global settings.
Remote Services
This section manages external services that the load balancer needs, such as DNS for resolving network names, NTP for synchronizing the system clock, and a Proxy service for using an external proxy for internal services. Any changes made to this section must be applied by clicking the Apply button. The Revert Changes button can be used to discard any modifications and revert to the previous configuration.
DNS
The Domain Name System (DNS) service is a directory service that translates domain names, such as google.com, into IP addresses, such as 8.8.8.8 or 8.8.4.4. This allows computers and other devices to communicate with each other over the internet.
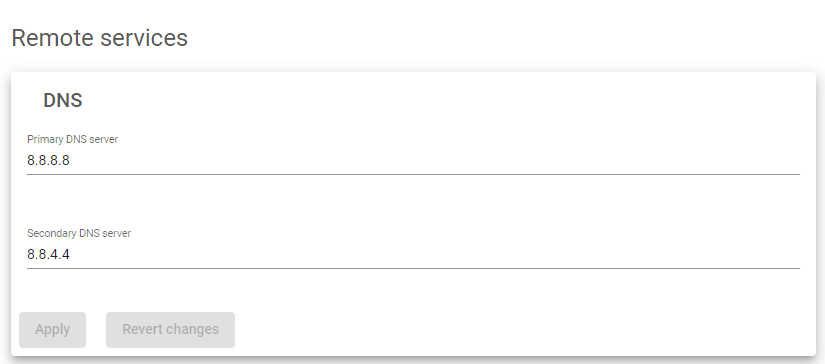
The DNS resolution configuration is stored in the file /etc/resolve.conf. This file specifies the IP addresses of the DNS servers that your computer should use to resolve domain names.
The primary DNS server is the first DNS server that your computer will contact to resolve a domain name. The secondary DNS server is used if the primary DNS server is unavailable.
Default DNS servers:
- Primary DNS server: 8.8.8.8
- Secondary DNS server: 8.8.4.4
NTP
The Network Time Protocol (NTP) service is used to keep the load balancer’s system clock synchronized with other time servers. This is important because many applications rely on accurate timekeeping, such as logging, authentication, and security.
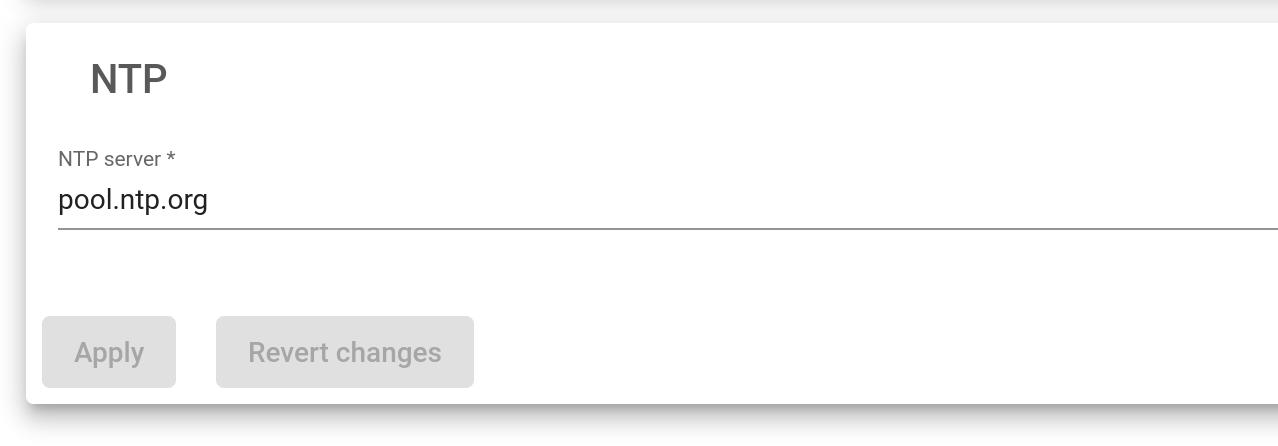
The NTP server is the computer that the load balancer will connect to to synchronize its system clock. The default NTP server is pool.ntp.org, which is a pool of public NTP servers that are maintained by volunteers around the world.
Proxy
The proxy service allows the load balancer to access the internet through a remote proxy. This can be useful for some services, such as updates, if they are configured to use a proxy.
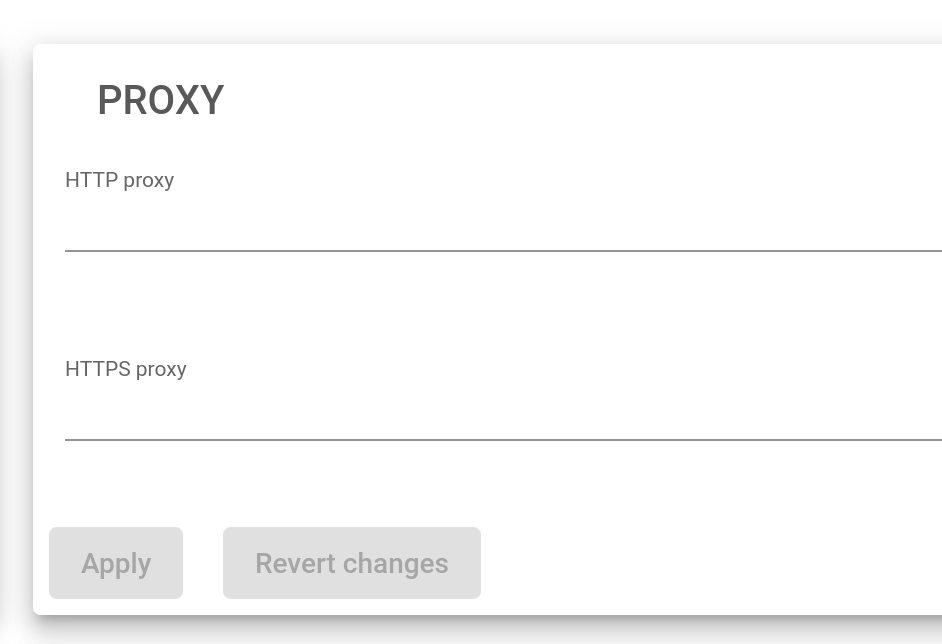
- To configure a proxy for HTTP requests, enter the full URL of an HTTP proxy in the HTTP Proxy field. For example, http://myproxy:80.
- To configure a proxy for HTTPS requests, enter the full URL of an HTTPS proxy in the HTTPS Proxy field. For example, https://myproxy:443.
Let’s Encrypt
Let’s Encrypt is a free, automated, and open certificate authority that provides trusted SSL certificates to websites. These certificates can be used to encrypt data transmission and prove the authenticity of a server.
Email: You can receive email notifications about your Let’s Encrypt certificates, such as when they are about to expire. This can help you to ensure that your website always has a valid SSL certificate.
Next Article: System | Cluster